In 2021, we witnessed the meteoric rise of NFT avatar projects and the trend has only increased in 2023. But what is a PFP NFT project? And, why are these cool PFP projects so popular? Basically, it all comes down to the perfect blend of art and blockchain technology.
PFPs and generative art NFTs are clearly cool enough to stick around. But, what do NFTs have to do with it? Well, NFTs make cool pfps for any social media, including Discord, Spotify, Instagram, Facebook, or Twitter. Whether you’re looking for the coolest new PFP ideas for girls, boys, in an anime style or in a 3d style, NFTs have you covered. Some people even use NFT PFPs as their LinkedIn profile pictures!
What is a PFP?
PFPs are also known as ‘Profile Pictures’. While some now define the acronym as ‘Picture For Proof’, it is currently disregarded as a false definition. The correct meaning is ‘Profile Picture’, or, profile pic.
What’s a Cool PFP Idea?
Well, you could download something from deviant art or right click save something from google images. But surely someone else will have done that already. For a truly unique and cool PFP, you should definitely consider an NFT! NFTs offer completely unique options to express yourself online. With an NFT PFP, you can guarantee you’ll have the coolest PFP of all your friends.
What are PFP NFTs?
NFT avatars, featuring a unique character, work as cool PFPs (profile pictures). Most of these projects are generative, meaning the NFT avatars are programmatically generated from a set of traits. These NFTs may grant holders access to an exclusive community. Additionally, they may offer offer access to real-life events, merch, games, or other perks too. Now, some of these PFP projects are so popular, they cost thousands of dollars.
How to find a cool PFP
While it may seem difficult finding the right NFT avatar for you, there are lots of aspects to help you make your choice. A good place to start is knowing the most popular projects. However, if you’re just looking for some cool artwork, you can also just explore an NFT marketplace to find your favorite. Just remember to do your own research and stay safe!
Coolest PFP Projects (and the most expensive)
From OG CryptoPunks to Doodles and more, here are some of the coolest PFP projects you must check out today.
CryptoPunks – The OG NFT avatars
Founded by Larva Labs in June 2017, CryptoPunks is one of the first-ever NFT avatar collections in the space. The collection of 10,000 NFTs features pixelated humans, apes, zombies, and aliens. To be honest, CryptoPunks set the standard for generative NFT projects that followed and enjoy an unparalleled iconic status in the NFT space.

Unsurprisingly, many of these have sold for millions of dollars—including this $23 million sale of CryptoPunk #5822. Now, Yuga Labs, the company behind BAYC, decided to acquire Cryptopunks. This means the collection should have many more perks to come.
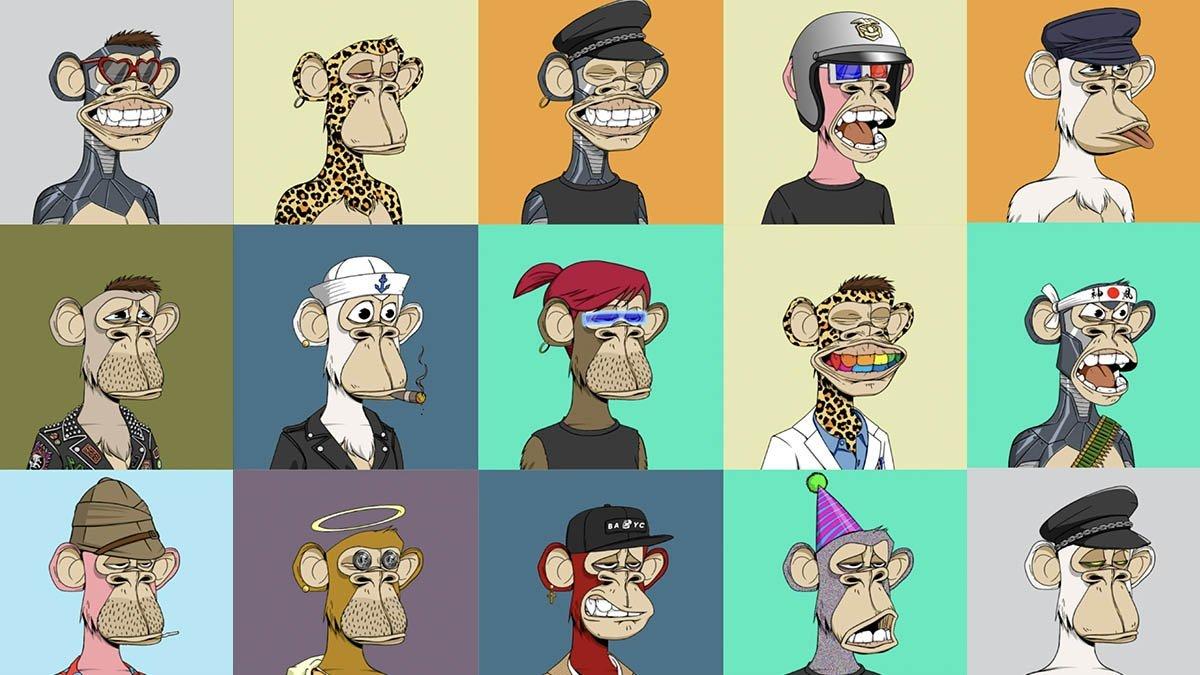
Bored Ape Yacht Club
Bored Ape Yacht Club (BAYC) enjoys a cult status in the NFT community. They even flipped CryptoPunks in December 2021. Actually, when they launched in early 2021, Bored Apes cost a mere 0.08 ETH. Since the launch, BAYC has built a strong community and a huge celebrity backing (including Justin Bieber, Snoop Dogg, Jimmy Fallon, and more).
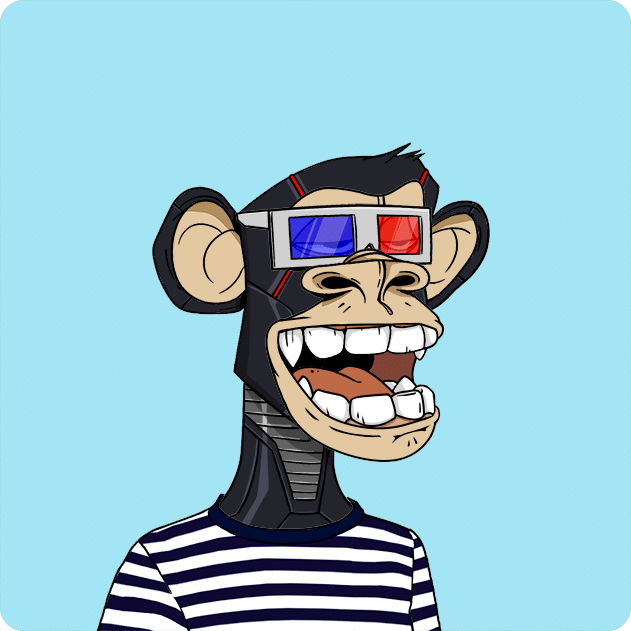
Unlike CryptoPunks, BAYC offers its members a range of benefits. This includes access to virtual and real-life events, metaverse lands, a private digital area called “The Bathroom”, and more.

They also released secondary collections Bored Ape Kennel Club and Mutant Ape Yacht Club (MAYC). MAYC in itself boasts around 256,000 ETH in trading volume and a 14.8 ETH floor! These are obviously a firm favorite for cool PFP lovers too!
Pixel Art PFP Projects
Nowadays, pixel art is a huge thing. Some of the most expensive NFTs in the world were just simple pixelart. The following projects are the biggest and most respected pixelart profile pictures in the industry. Check them out!
Moonbirds
These pixelated owls, or “birbs” are the first PFP project by Proof Collective. The private, members-only collective of NFT collectors launched the project, led by Kevin Rose. Actually, you can use any of the Moonbirds NFTs as your PFP WITHOUT BUYING ONE! That is because they rescinded their IP rights for cc0 rights instead.

Put simply, Moonbirds is a collection of 10,000 pixel art owls on the Ethereum blockchain. Each of these feathered avatars is unique and comes with a range of traits with varying rarity. More importantly, each NFT gives you access to private club membership and other benefits the longer you hold the NFTs. Now, they also have a new PFP collection, Moonbirds’ Oddities, in partnership with Gremplin.
CyberKongz
CyberKongz has established itself in the space as more than a mere NFT avatar project. The project started as a genesis collection of 1,000 CyberKongz in March 2021. Soon after, they released 4,000 Baby CyberKongz. But, it was the launch of CyberKongz VX NFTs that put the spotlight on the project. The 3D Voxel collection of 15,000 models serves as playable NFTs in CyberKongz’s metaverses.
Currently, the team also boasts their very own game, Play & Kollect. For this, they have partnered with Chainlink to add randomized in-game features.
The Cutest PFP Projects
Cool Cats

Cool Cats is another blue-chip PFP NFT project to keep an eye on. These randomly generated NFTs hit the Ethereum blockchain in July 2021. Each NFT in the collection is unique with different traits such as body, hat, face, and outfit. With their simple and cute 2D artworks, Cool Cats is much beloved by collectors across the globe.
Since its launch, they have struck up some important partnerships, including with TIME magazine, GHXSTS, and even the Macy’s Thanksgiving Day Parade. Their whole NFT ecosystem includes; Cooltopia, $MILK, Cool Pets and- soon – a whole host of other Cooltopia characters.
Doodles NFT

Compared to the others, Doodles is a more recent NFT avatar project enjoying blue-chip status. Launched last October, the Pastel-hued, line-drawn characters are one of the most loved NFT avatars in the space. The collection of 10,000 NFTs features humans, cats, aliens, pickles, and more.
Besides, the fully doxxed Doodles team is made up of experts in the field. While Scott Martin ( popularly known as ‘Burnt Toast’) is an acclaimed Canadian illustrator, Evan Keast and Jordan Castro worked with the OG CryptoKitties NFT collection.
Apart from the team’s expertise, several other factors helped in the collection’s growth. This includes the creative and diverse artwork, the team’s community-first approach, holder benefits, and more. Recently, they even launched a new collection—Space Doodles, for all current holders.
Weird and Funny PFP Projects
Goblintown
Goblintown.wtf is a collection of 10,000 NFTs featuring all sorts of unsightly creatures. Their unique characters include trolls, dragons, wizards, mosquitoes, and even the ugly Kevin NFT we’d all like to forget.

Goblintown struck a chord with the bear market culture within the NFT Twitter. Essentially, its humorous take on the market conditions catapulted the project into its star status. Now, the goblins enjoy blue-chip floor prices and a dedicated community that loves to laugh.
Coolest Profile Picture NFTs for Girls and Women
World of Women – meet the coolest female NFT avatars
- Collection size: 10,000
- Current floor: 7.2 ETH
- OpenSea trade volume: 55,800 ETH
World of Women (WoW) is one of the leading female-led avatar NFT projects in the space. Launched in July 2021, WoW was a breath of fresh air in a market filled with apes, cats, and other animals. In fact, WoW is one of the first-ever NFT collections focusing on diverse female avatars—something extremely lacking in the NFT space.

The 10K collection topped charts this year after celebrity endorsements from Reese Witherspoon, Eva Longoria, and others. The collection also regularly donates to women-led organisations and sustainability-focused organisations. Apart from this, WoW supports one-of-one crypto artists through its WoW Fund.
Women With Weapons
Women And Weapons is a diverse and inclusive NFT project with a firm focus on art. The art is diverse, featuring a treasure trove of ‘badass’ women. And with them, of course, an array of different weapons.
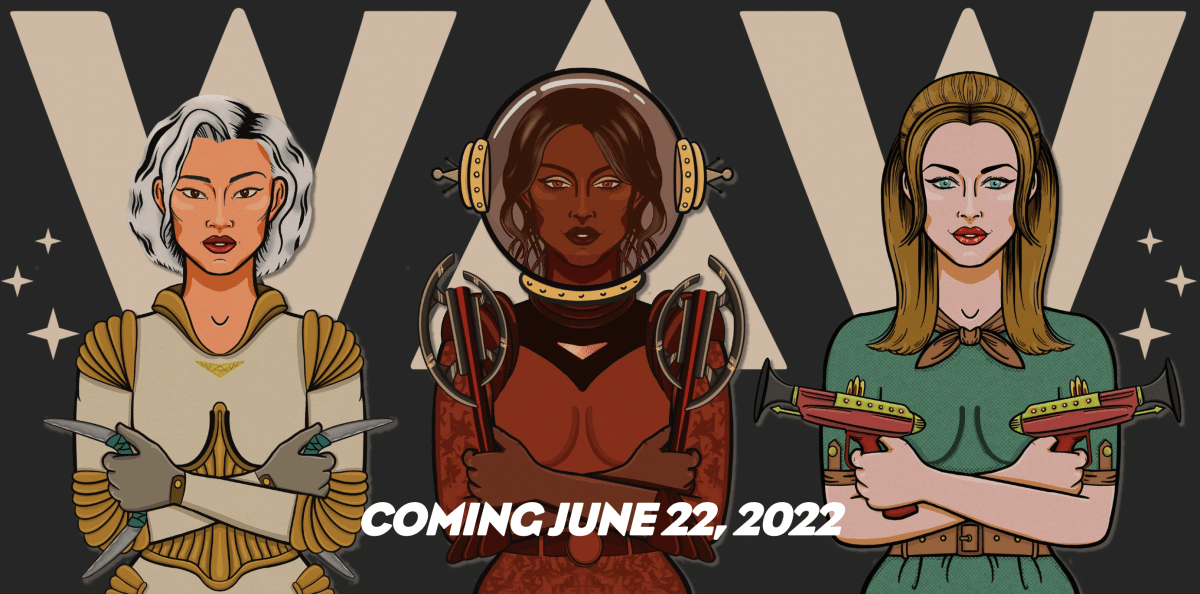
Iranian-American artist Sara Baumann is the co-founder and lead artist behind the project that offers a creative and inclusive community, aiming to empower women worldwide.
Profile Picture NFTs for Boys and Men
There are a bunch of NFT projects aimed at specific genders. Here are some cool PFP collections for men and boys:
CryptoDads
In short, CryptoDads is a collection of 10,000 unique, randomly generated NFTs dwelling on the Ethereum blockchain. In terms of art style, it resembles the animated series, ‘Bob’s Burgers.’
“Each dad found themselves in the midst of a midlife crisis and fell into the dark abyss of shit coins and expensive jpegs of rocks,” the project’s website notes. “Some made it out with diamonds, and others never recovered.”
Cryptomories
While cryptomories are not exclusively for men, they do donate money to men’s mental health charities. Supporting cryptomories helps support men’s mental health! CryptoMories is a collection of 10,000 adorable little skeletons.

They say they are here to “remind you that life is good, that there are a lot of amazingly kind people, and that you are one of them.” To explain their name, it’s derived from “memento mori”. In short, this is a Latin saying meaning “remember you die”.
Old School NFT PFP Projects
Maybe you want to have a piece of NFT history? These are the most popular NFT projects people still like to use as profile pictures a year after their launch. While some of them aren’t so expensive any longer, they are still great options for showing off something cool and unique on social media.
Gutter Cat Gang
Gutter Cat Gang is one such project still surviving from the NFT boom in 2021. Owing to their popularity, the project followed up with several other collections— Gutter Rats, Gutter Dogs, and Gutter Pigeons. All the secondary collections also have a capped supply of 3,000 NFTs each.

Besides, the project has built up strong lore set in the year 2050. Basically, cats have taken over the future society after an apocalypse. What’s more, the project has its own ‘Gutter Merch Collection’ featuring dad hats, hoodies, beanies, tees, and more.
DeadFellaz
Launched in August 2021, DeadFellaz is one of the top undead-themed PFP projects. The collection of 10,000 green-coloured cartoon zombies is generated from over 300 traits. Then, thanks to the team’s efforts to give back to the community, the project became quite popular in the space
Additionally, the cool PFP collection has its own ERC-20 token, called DEADFELLAZ20 and a “Deadzone 13” in Decentraland. Next, the DeadFellaz team launched a new companion collection of 13,000 NFTs called DeadFrenz. Accordingly, these NFT pets were a huge hit, with many collectors priced out of the original collection. If you want to know more, check out our interview with Betty, the co-founder of DeadFellaz.
SupDucks
Launched last July by Latin American NFT artist, Franky Aguilar, SupDucks had sold out in 48 hours. The 10,000 unique NFT avatars are generated from hand-drawn traits including mouths, eyes, skins, backgrounds, clothes, and hats.

With the simple and adorable artwork, SupDucks immediately struck a chord with the NFT community. With a keen focus on community-building, the team has planned many things for their members, including a merch shop and a 2D SupDuck metaverse. Check out our interview with FrankyNines for more information!
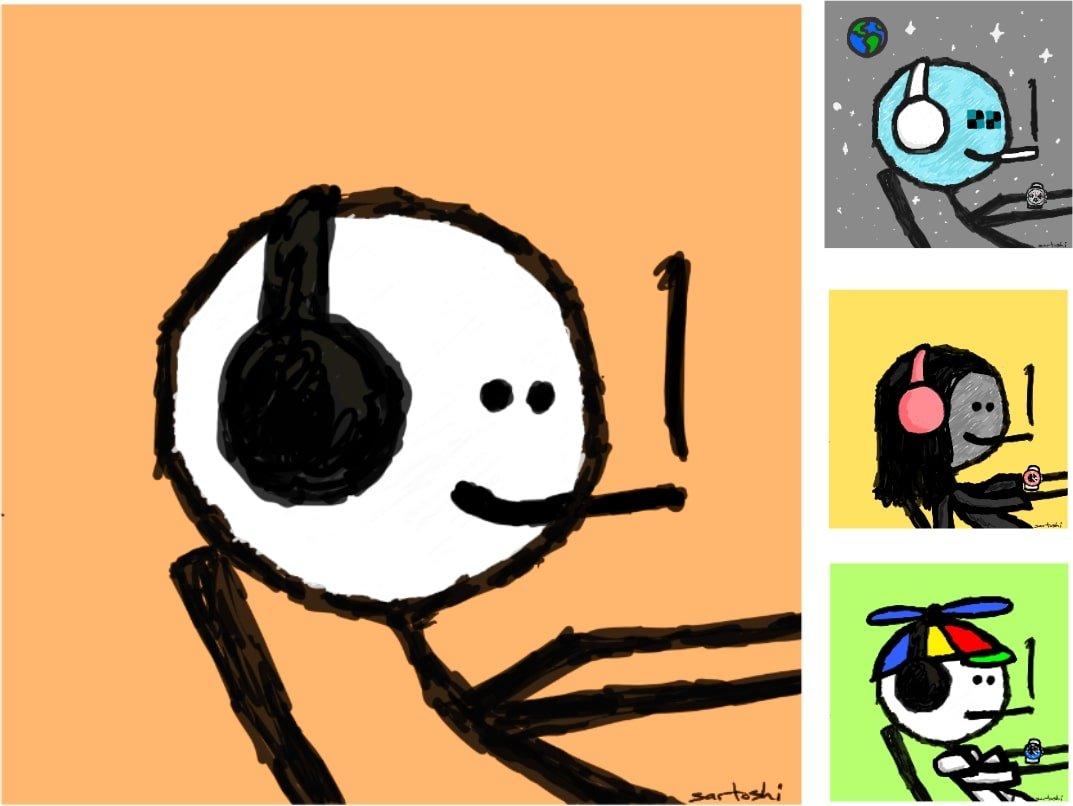
Mfers – NFT avatars from Sartoshi
Mfers is the brainchild of acclaimed meme creator, Sartoshi—a spin on the words ‘art’ and ‘Satoshi’. The collection of 10,021 stick-man NFTs is generated completely from Sartoshi’s hand-made drawings. Of course, the Mfers collection too takes inspiration from meme culture. The NFTs dropped in November 2021 and were such a huge hit that they sold out in under 10 minutes!
Bitcoin PFP Avatars
Finally, let’s take a look at Bitcoin NFTs. With their recent surge in popularity, there are lots of cool PFPs to choose from here.
Ordinal Punks
Ordinal Punks is a collection of Bitcoin NFTs that pays homage to the renowned CryptoPunks collection on the Ethereum blockchain. Each Ordinal Punk NFT represents an exclusive and distinctive digital artwork. With a total of 100 unique PFPs, this collection stands out as a testament to creativity and individuality. Notably, these PFPs are meticulously minted within the initial 650 inscriptions, ensuring their complete on-chain presence on the Bitcoin blockchain.

Taproot Wizards
Next, let’s take a look at Taproot Wizards, a captivating collection of 2,121 unique and wizard-themed Ordinals. This extraordinary collection has garnered widespread acclaim for its innovative approach in celebrating Bitcoin’s rich history, notably through the inclusion of the legendary Bitcoin Wizard.
The Bitcoin Wizard, initially conceived as a drawing-turned-meme by the talented artist mavensbot, first made its debut on the renowned r/Bitcoin subreddit. Portraying a wizard accompanied by the iconic phrase “magical internet money – join us,” this image swiftly captured the imagination of the crypto community.
Bitcoin Frogs
Finally, let’s take a look at newcomers, Bitcoin Frogs. Markedly, Bitcoin Frogs is a brand new collection of 10,000 one-of-a-kind NFTs that showcases delightful artwork featuring lovable frog characters. Since its exciting debut in late February, this collection has taken the NFT world by storm.
Ultimately, when it comes to NFT avatars, you are spoilt for choice. But, whichever cool PFP you choose, make sure to do your own research before taking the leap. Remember, NFTs are speculative assets subject to market risks.
All investment/financial opinions expressed by NFTevening.com are not recommendations.
This article is educational material.
As always, make your own research prior to making any kind of investment.