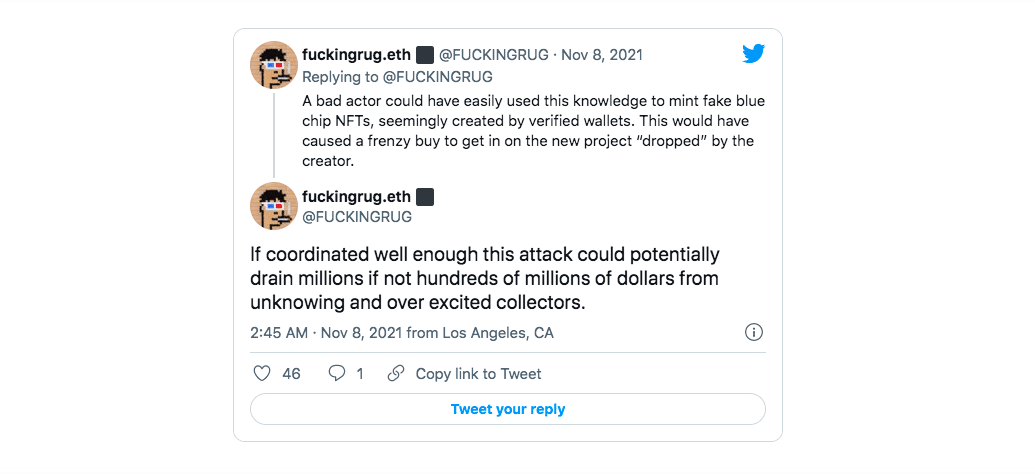
OpenSea is under fire once again because of a security breach. This time a white hacker discovered a fatal flaw in the codebase of the biggest NFT Marketplace by trade volume. This was a major save because the bug could have allowed fraudsters to create fake blue-chip NFTs (think BAYC). Then, create a “frenzy,” ultimately draining millions, if not hundreds of millions.
Hero of the day is Twitter user F*****GRUG, who develops and builds smart contracts for NFT and Web 3.0 as part of RUG.TECH.

More about OpenSea’s Security Breach
As described by the developer, the error indicated that the bug made it “possible to mint NFTs that appear to be created by any ETH wallet you choose” without consent or approval from the wallet owner.
In a tweet, he slammed OpenSea and claimed that it’s not giving security the attention it deserves. He said, “Finding bugs is often lucrative, especially in the blockchain. Companies are willing to pay millions for the discovery of mission-critical bugs. Opensea, however, pays next to nothing for discovering potentially platform-ending errors in their codebase.”
The Trend: White Hackers and Bounty
Typically, platforms and apps reward those who identify bugs with a bounty. Unfortunately, it wasn’t a pleasant experience for F*****GRUG. OpenSea initially offered 3 ETH but they promised a bigger reward considering the critical and high-risk nature of the bug. However, they rescinded the bonus bounty even though the developers helped in completing the troubleshooting.
Obviously, the white hackers were disappointed. In a tweet, he narrated how things went down between his team and security lead Daniel Roelker. “After we were finished helping them troubleshoot, Dan sent this, doubling down on the initial 3 ETH. They waved a higher bounty over our heads while we were actively helping them and then pulled back when the work was done. Awesome.”
In an email, Roelker defended OpenSea’s move by citing that the developer’s reports “fall in line with a lot” of their fraud efforts, indicating it does not solve the “collection owners vs. creators.”
OpenSea’s Track Record: Bugs and Security Breach
Just last September, OpenSea faced another security issue. The vulnerability allowed hackers to hijack user accounts and steal entire crypto wallets of users by sending malicious NFTs. Users have been complaining about zero balance in their crypto wallets, a result of accepting a gift on the OpenSea marketplace.
Once the user views the malicious NFT, a pop-up will appear from the storage domain, asking for a connection to the target’s cryptocurrency wallet. Not suspecting the pop-up, the victim clicks to connect their wallet to claim the gift (NFT), allowing the hacker access to the user wallet.
Check Point Research (CPR) immediately disclosed its findings to OpenSea on Sunday, September 26, 2021. In less than an hour of disclosure, the platform fixed the issue and verified the fix. According to the press release, CPR worked closely and collaboratively with the team to ensure the fix worked correctly. OpenSea was very responsive and shared SVG files containing iframe objects from their storage domain, so CPR could review together and ensure all attack vectors were closed.
This incident is a reminder to all crypto and NFT users to remain vigilant!
All investment/financial opinions expressed by NFTevening.com are not recommendations.
This article is educational material.
As always, make your own research prior to making any kind of investment.








