Now, many music stars are minting their music as NFTs. While music legends have everything they need at their disposal, that may not be the case for everyone – especially emerging artists. Are you a musician looking into NFTs? Let’s talk about where to find NFT music, why NFT music is so interesting and the best NFT music marketplaces in the industry right now. Plus, we’ll tell you; how to mint and sell your NFT music, plus, the top types of music NFTs on the market. But firstly, exactly what are music NFTs are in the first place? And which NFT musicians should you be following? Let’s take a look:

What are music NFTs?
NFTs are digital assets that represent a real-world or digital object using blockchain technology. They are one-of-a-kind, akin to rare art pieces. Thus, NFTs are unique assets of which the authenticity and ownership can be easily verified.
NFTs can represent a range of digital assets, including music. With NFTs, musicians across the globe can sell their exclusive songs for what they’re worth and connect with fans worldwide.
Music NFTs aren’t limited to singles or album releases. Artists can even sell virtual or physical merch, wearables for metaverse avatars, concert tickets and exclusive behind-the-scenes footage. Plus, producers can sell beats, songwriters can sell lyrics as NFTs, and much more.

What is this NFT Music Craze All About?
Currently, many emerging artists struggle to earn a living by selling their music. In fact, they may have to depend on middlemen like record labels, who charge exorbitant sums, and may not even be accessible for upcoming artists.
Accordingly, NFTs present an opportunity to give the power back to the artists. Artists can now sell directly to their fans, without the hassles of middlemen, and earn what they deserve. Yes, that means no more record labels and managers eating into musician’s profits!
Secondly, NFTs allow artists to set royalties on their music, meaning the creator earns a percentage every time their NFT is resold.
As American hip hop recording artist, Supa Bwe noted, indie artists now have the chance to remove the “risk of being undervalued/cheated/reliant on/by corporate entities.”

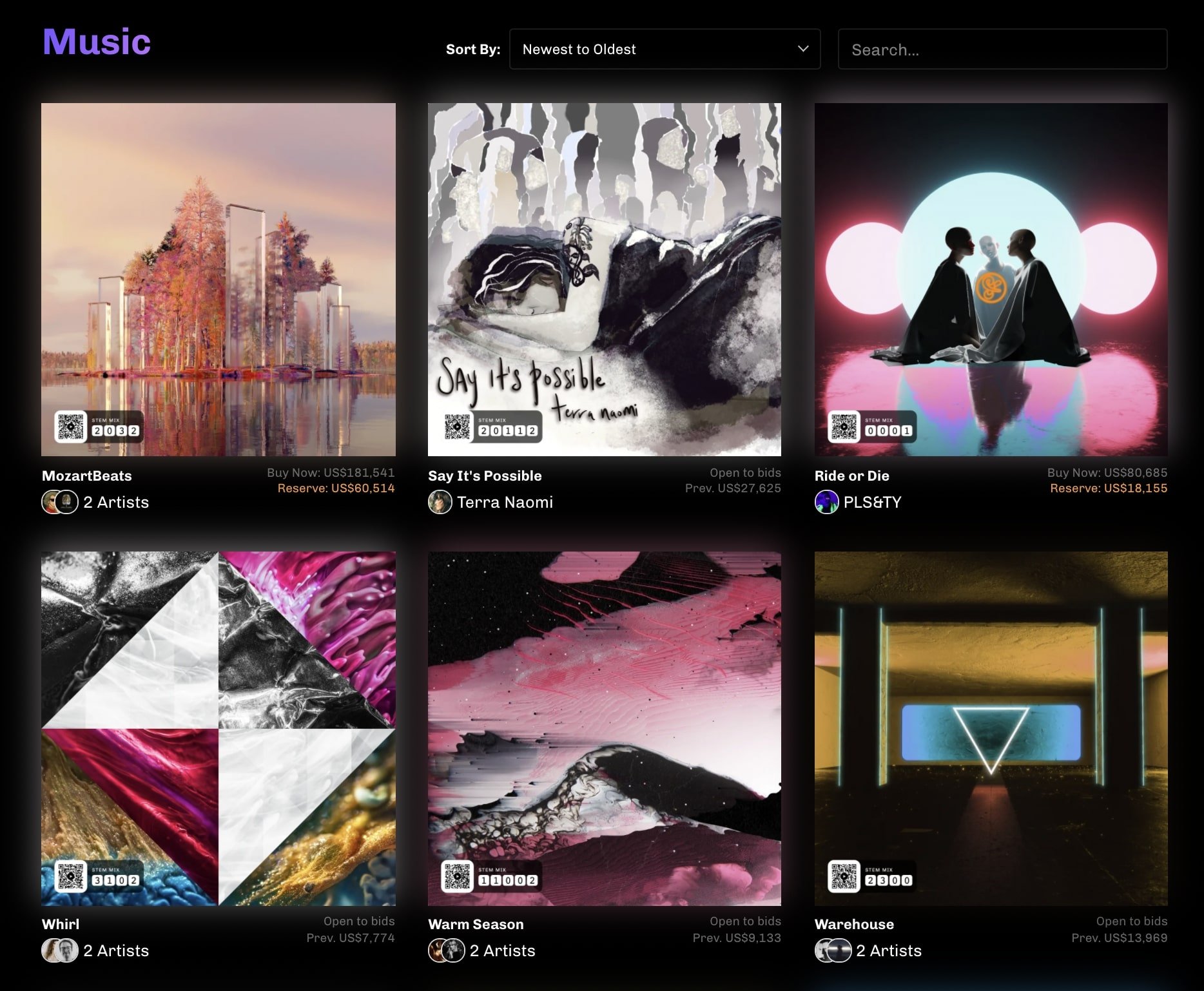
Where To Buy Music NFTs: The Best NFT Music Marketplaces
There are plenty of Marketplaces to Buy Music NFTs. Although the biggest platforms like Opensea and foundation also support music NFTs, there are a few NFT Marketplaces for music, that focus solely on that.
Catalog
Back in March 2021, Zora, a decentralized NFT platform, partnered with 20 emerging artists to launch Catalog NFT Music Marketplace. Basically, Catalog is a “record press, an auction house, and an open music library”.
It calls itself “a new medium for music.” Incredibly, it offers artists 100% of their sales. As a dedicated music NFT marketplace that truly helps artists to reclaim music ownership, Catalog is growing in popularity in the music industry.
Within two months of its launch, the marketplace onboarded acclaimed artists like Richie Hawtin, Laxcity, SALVA, and Boys Noize, among others. Today, it also boasts artists such as Pussy Riot and Haleek Maul, who sold a track for $75,000 on the platform.
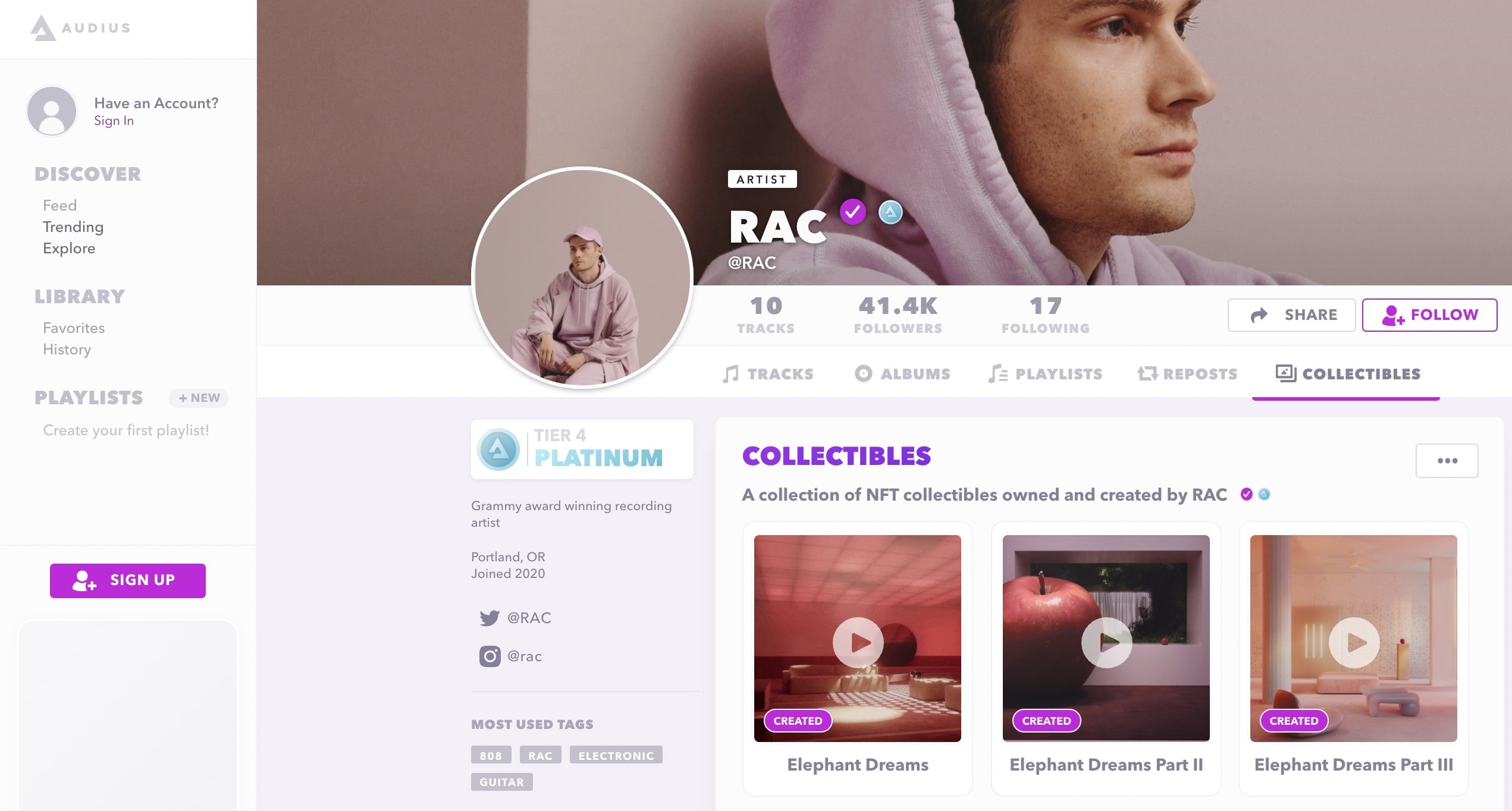
Audius
Audius is a California-based decentralized music streaming platform. It is basically like a decentralized version of Spotify based on the Ethereum and Solana networks. This means, the platform is run by a community of artists, fans, and developers and allows artists to upload their music on the platform free of cost.
It also offers AUDIO tokens for governance capabilities. What’s more, the platform is backed by some of the top names in the industry, including Katy Perry, Nas, The Chainsmokers, and Jason Derulo, among others.
Unlike the platforms mentioned above, Audius does not allow you to mint NFTs. It, however, offers ‘Audius Collectibles’, where music artists can display their NFTs on their profile. Musicians can connect multiple crypto wallets and display NFTs from a range of marketplaces like Rarible, SuperRare, and OpenSea.
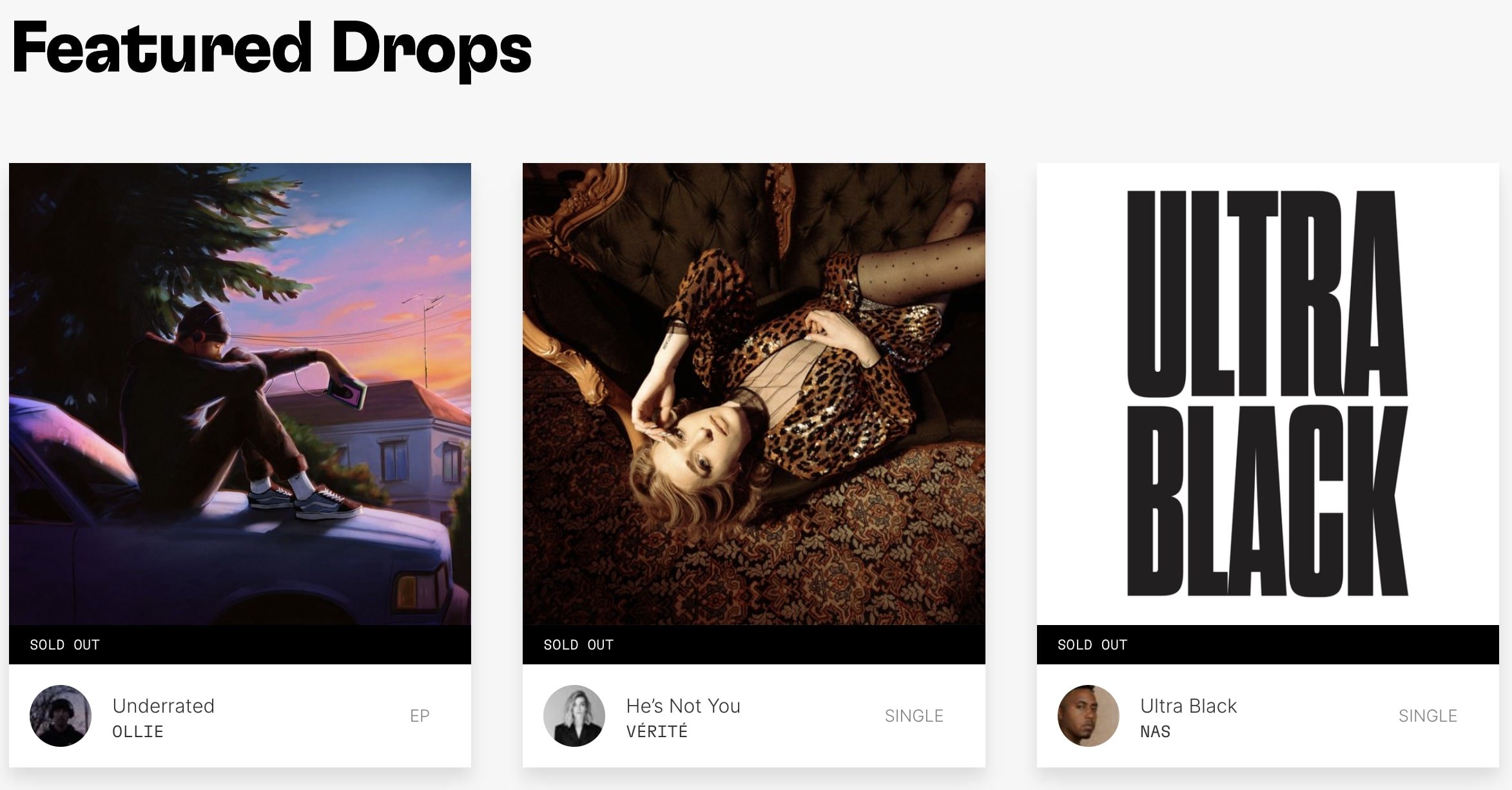
Royal Music NFT Marketplace
Another music NFT-focused platform you can check out is Royal. The platform works in a simple way—musicians can sell royalty ownership to their songs along with special perks. Then, the collectors can buy the royalty ownership directly from the artists through tokens. To sum up, every time the artist earns via music streaming, so does the collector.
“Royal opens the door for artists to retain independence and creative control as fans fuel their careers,” the platform notes. Additionally, it is up to the artists to decide the percentage of royalties they want to sell. The royalty percentage also depends on the token’s tier. The higher the tier, the larger the royalty payout that the collector receives. Besides, the artist can add any extra benefits that they want to the token. This ranges from fan experiences to special tracks and digital art.
Some of the other NFT platforms you can check out are Tezos-based Hic et Nunc (MP3s, MP4s, and WAV), Mintbase (MP3 and MP4), Cargo (MP3 and MP4), and music NFT platform Opulous.
Async Music
Async Music is an invite-only marketplace that focuses on programmable music, which changes over time. It is a vertical of Async Art, Ethereum’s platform for programmable art. According to the website, it allows users to create a single “Master Track NFT” which comes with individual components, “Stem NFTs”. While the “most hardcore fan” will own the 1/1 Master, the Stems will go to the other fans. As of now, the platform only supports MP3 files.
Sound.xyz
Sound.xyz is an NFT music platform that aims to solve two main issues in the music industry. First of all, while a majority of the produced songs go unheard, the top 1% of artists get 90% of streams. Next, artists barely earn $0.003 per stream and have to struggle to make ends meet.
Thus, Sound was set up to solve these problems and support the next generation of artists. It describes itself as a platform created “for a more collaborative music movement, built on web3 technology and values.”
The platform enables artists to launch a “listening party” for new releases through a series of limited edition NFTs. Owning the NFTs gives fans the ability to support the artist by publicly commenting on the song. Additionally, artists have the option to add other perks to the NFTs, such as exclusive listens of unreleased songs or concert tickets.
Myx
Myx is a “revolutionary Web3 music space for artist and music lovers”. A streaming and NFT platform, Myx aims to bridge the gap between artists and their fans. Basically, artists can release their tracks and collections as either 1/1 or multiple edition NFTs on the platform. Then, the NFTs will be automatically available on OpenSea. Because of this, artists will get a chance to earn from secondary sales.

Myx also offers a feature called “Pods”, via which fans can invest in their favourite artists and earn along with them. Essentially, Pods is a tool that allows different individuals to come together for music collaborations and earn together. Each collaborator will earn a revenue proportional to their Pod ownership.
Due to decentralised streaming, the platform claims that artists can earn up to three times what they earn from streaming on Spotify. In addition, Music NFTs on the platform are secure and stored with IPFS. Currently, Myx is in a soft launch phase. It will launch streaming in Q2 of 2022.
How To Sell a Music NFT
When considering if you want to sell your music as an NFT, an important thing to note is copyright law. If you don’t own the complete recording and publishing rights of a song, you’ll have to first get the license to use it as an NFT. Jay-Z, for instance, sued his former partner for trying to sell an NFT allegedly consisting of the singer’s 1996 album “Reasonable Doubt”.
Next, you’ll have to choose where to mint and sell your music as an NFT. Firstly, you should check out the aforementioned music NFT marketplaces. However, many of them have strict entry requirements. Fortunately, many generic NFT marketplaces also support audio files and can get you off to a great start as an NFT musician.
Where To Sell Music As An NFT
These martketplaces all have less strict recquirements when it comes to selling your music as an NFT. Each of them have different capabilities so make sure to check before you mint your song as an NFT.
OpenSea is the largest NFT marketplace in the world, having amassed over $9.5 billion in trading volume to date (at the time of writing). When it comes to music NFTs, you can mint file types MP3, MP4, and WAV.
Then, Rarible is another top NFT marketplace and is currently sixth on DappRadar’s list of top all-time marketplaces by trading volume. It is simple, has an attractive interface, and has its own ERC-20 governance token, called RARI. It supports file types MP4 and MP3 of a maximum size of 100 Mb, perfect for selling your first music as an NFT.
Additionally, Nifty Gateway, owned by cryptocurrency exchange Gemini, is another NFT marketplace popular among musicians. The platform has hosted NFTs of music stars including deadmau5, Grimes, and Steve Aoki.
Finally, Foundation is another NFT platform that has a meticulous application process in place to accept artists on the platform. For music NFTs, it supports the MP4 file format. In the past, Foundation featured top Musicians like Aphex Twin and Pussy Riot.
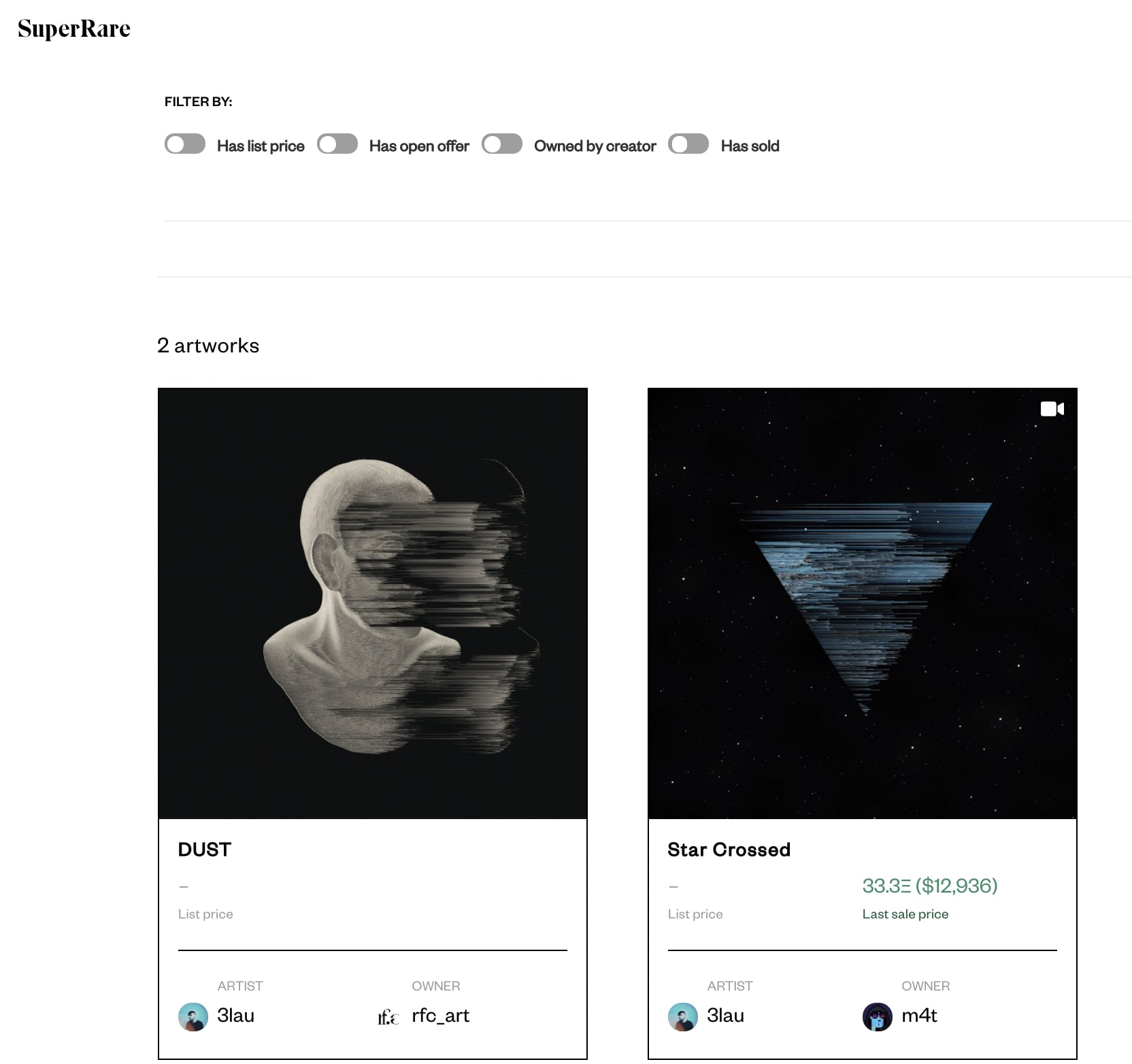
Famous Musicians with NFT Collections
Electronic dance music producer and DJ, 3LAU sold his album as an NFT in 2021 for over $11 million. Similarly, in March 2022, British MC and Rapper, Big Narstie dropped his latest single ‘Gas the Set’ as an NFT. Australian singer-songwriter Sia too has an NFT collection to her name, called Siaverse. On the other hand, American rapper, singer and songwriter, Doja Cat sold her NFT collection for over $188,000 late last year.
In the meantime, Snoop Dogg recently announced his plans to make Death Row Records into an NFT music label. Essentially, he will be “putting out artists through the metaverse.” Then, in August 2021, The Dallas Symphony Orchestra dropped classical-music-themed NFTs complete with a full concert video, behind-the-scenes videos, and VIP access to a reunion concert too!
What is Generative Music?
Much like generative art NFTs found their popularity, many also consider generative music NFTs the next meta. As opposed to the common choice of dropping albums as NFTs, generative music NFTs are generated by an algorithm. Most often, these NFTs offer music that adapts real-time, depending on a situation or some built-in function.
Let’s take a look at some of the popular generative music NFT projects in the space!
The Ghost of Frank Dukes
The Ghost of Frank Dukes features 9,999 pieces of original generated audiovisual artworks. The project is the brainchild of a group of creators “exploring the future of music in web3 and beyond”. All the music NFTs in the collection are algorithmically generated from decades of source material produced by music producer, Frank Dukes. The project has a solid roadmap in place, with future developments such as a Ghost Downloader, Ghost Sample Generator, Ghost Editor, and more.
Omgkirby Genesis – Lo-fi generative music
Omgkirby Genesis collection is perfect for those who love lo-fi music—music with many imperfections. The collection includes 3,000 unique pieces of generative lo-fi music created from a combination of algorithmically-assisted music and hand-drawn art. The collectors get full ownership of the song, complete with the master recording and publishing rights. Besides, all members will become part of the omgkirby DAO, where they will have the power to make decisions on the omgkirby treasury.
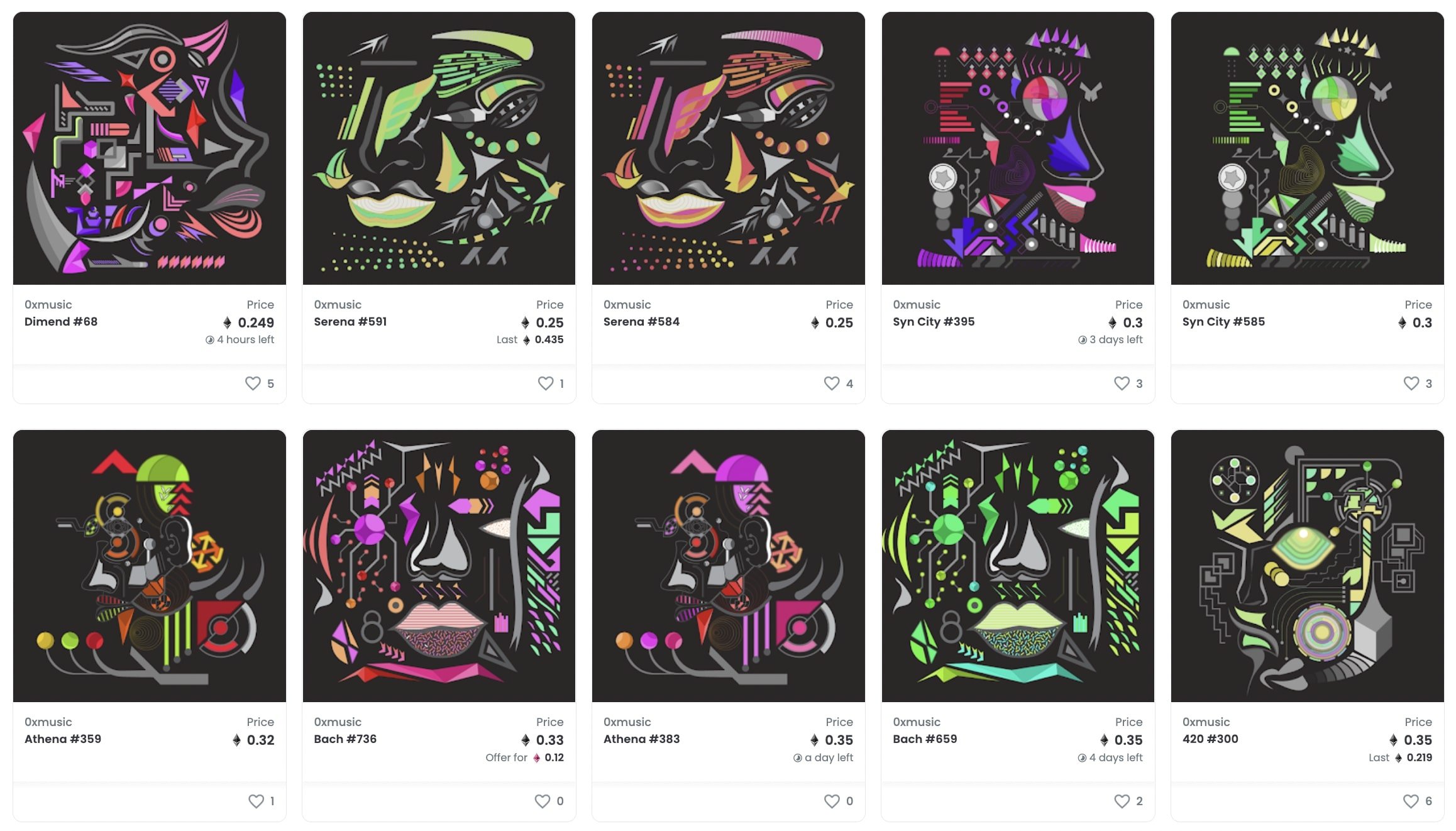
0xMusic – Generative “DJs”
0xMusic is a collection of “0xDJs”—generative audiovisual DJs that create a new piece of music every time you press play. Based on the Ethereum blockchain, each 0xDJ can generate an infinite number of music pieces in real-time. On pressing the play button, the associated image comes alive with a brand new piece of music. The piece will continue playing till you hit the button again. Then, the music will be destroyed forever, making way for a new song.
Beatboxes by Zeblocks: Generative music with VR
Another interesting generative music NFT project to check out is Beatboxes by Zeblocks. The project claims to be the first “fully immersive VR audiovisual generative art” on the Ethereum network. The collection features a total of 841 generated unique rooms that collectors can enjoy using a VR device. Needless to say, each room or Beatbox is an NFT. The idea behind the project was to create a space where users can “escape their reality for a moment” and enjoy the artwork. The NFTs are available on OpenSea.
NFTs have opened up an all-new means for musicians to earn, engage with fans, and amass a global following. While these digital assets offer a promising future for artists, it is important to do your due diligence and analyse the market before dropping your first NFT.
All investment/financial opinions expressed by NFTevening.com are not recommendations.
This article is educational material.
As always, make your own research prior to making any kind of investment.